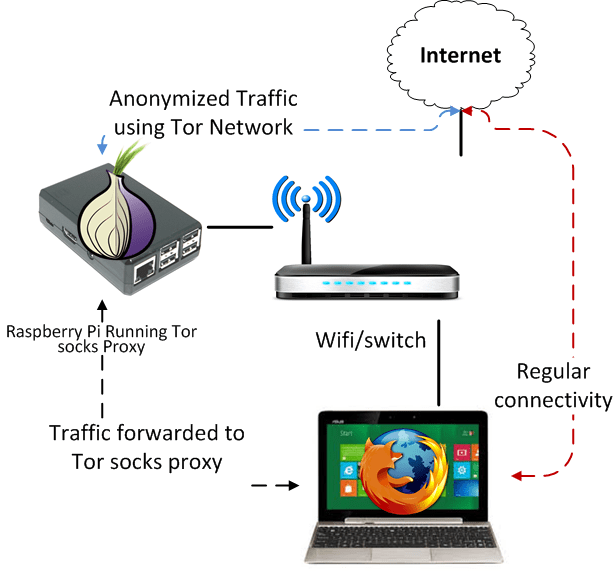
Setting up Tor socks Proxy on Raspberry Pi
The goal is to setup your Raspberry Pi as a tor socks Proxy and help you setup a desktop web browser to use the tor socks proxy. This shall allow you to browse anonymously without having to install tor on your desktop machine. You may use other applications with this tor socks proxy installed on… Continue reading Setting up Tor socks Proxy on Raspberry Pi